Cryptocurrency Theft: The Scale of the Problem
The cryptocurrency security landscape continues to evolve. Despite rising losses in digital assets, the blockchain infrastructure itself is gradually becoming more secure. At the same time, the sources of risk are also evolving: threats can arise from vulnerabilities in software and protocols, as well as from the compromise of keys, devices, or user credentials.
2025 was a record year for hacker attacks and incidents. However, the largest losses were caused not by blockchain failures, but by operational errors: compromised passwords and private keys, infected devices, employee manipulation, and fake support services. Human error, rather than technological flaws, is increasingly the cause of theft. At the same time, the focus of criminals is shifting. While protocols and infrastructure were once the primary targets, attackers are now increasingly targeting private users.
In 2026, attacks on crypto services and individual users continued. In March alone, there were approximately 20 major hacks totaling $52 million. Notable incidents included an attack on the Resolv crypto protocol, which resulted in the theft of $25.3 million, as well as the theft of nearly $18.2 million from a Kraken exchange client who fell victim to targeted social engineering. One of the largest incidents of the spring was the hack of the Solana-based DeFi platform Drift Protocol. On April 1, an attacker withdrew at least $280 million from the protocol.
Major hacks of protocols, exchanges, or wallets typically make it into the public domain, while many smaller thefts go unnoticed. Every day, users with relatively small amounts—from a few hundred to tens of thousands of dollars—fall victim to fraudsters. These cases rarely receive publicity, but collectively account for a significant share of losses in the crypto market.
The most common methods of cryptocurrency theft
Phishing sites and fake interfaces
Phishing websites and fake interfaces remain one of the most common methods for stealing cryptocurrency. Fraudsters create copies of popular services—exchanges, DeFi protocols, or wallets—that are visually almost indistinguishable from the original. Users are directed to these websites through advertisements, social media links, search results, or messaging. They are then asked to connect a wallet, enter a seed phrase, or confirm a transaction. This allows the attackers to access funds or withdraw them through a smart contract.
Sometimes phishing pages don't mimic the entire service, but only a specific window—for example, a login form, an airdrop page, or a wallet connection interface. The user may not notice the substitution, especially if the website looks identical to the original.
To reduce the risk, we recommend always checking the website address in your browser and using only saved bookmarks, rather than clicking links from messages or ads. It's also important to never enter your seed phrase on third-party websites and carefully read the contents of transactions before confirming them in your wallet.
Malicious extensions and programs
Malicious extensions and programs are another common method of stealing cryptocurrency. Criminals distribute fake browser extensions, wallets, or utilities that appear to be legitimate. Sometimes they disguise themselves as popular services or useful apps—for example, tools for trading, price tracking, or DeFi.
Once installed, such software can monitor user activity, spoof addresses when copied, intercept wallet data, or request access to private keys and seed phrases. In some cases, malware gains system access and reads information directly from the device's memory or files.
To reduce the risk, we recommend installing extensions and programs only from official sources and verifying the developer before installing. You should also avoid little-known tools, update your system regularly, and use a separate browser or device for accessing crypto wallets.
Compromise of seed phrases and private keys
Compromising a seed phrase or private key is one of the most direct ways to lose cryptocurrency. This data grants complete control over the wallet, so obtaining it by an attacker effectively means losing access to the funds. Most often, leaks occur through phishing sites, malware, storing keys in cloud services, or sending them via instant messaging and email.
Sometimes, users enter the seed phrase themselves on fake "wallet recovery" pages or give it to scammers posing as support staff. In other cases, keys can be stolen from a device infected with malware.
Store your seed phrase and private keys only offline—for example, written down on paper or on a hardware device. They should not be entered on third-party websites, sent online, or stored in notes, cloud services, or screenshots. For additional security, we recommend using hardware wallets and dividing your funds between multiple addresses.
Social engineering and social media fraud
Social engineering is one of the most effective methods for stealing cryptocurrency. In these schemes, attackers don't hack systems directly, but instead attempt to deceive users into accessing their funds. They may pose as exchange employees, project representatives, well-known traders, or even acquaintances whose accounts have previously been compromised.
Scammers often contact victims through social media, instant messaging, or comments under posts. They offer "help" with transferring funds, participating in an airdrop, an investment opportunity, or an urgent solution to an account issue. During the conversation, the user may be asked to install a program, click a link, connect a wallet, or disclose confidential information.
It's important to remember that crypto project and exchange employees never request seed phrases or private keys. Any offers in private messages should be verified through official channels. It's also recommended to ignore "investment offers" from strangers and avoid clicking on suspicious links, even if they come from familiar accounts.
Address spoofing attack
An address spoofing attack is another common cryptocurrency fraud scheme. Fraudsters create an address that is visually very similar to an address previously used by the user. They then send a microtransaction of a small amount, sometimes just a few cents, to the victim's wallet. This transaction is recorded in the user's transfer history.
Later, the user can copy the address from the list of recent transactions, assuming it is the same recipient as before. If they don't notice the substitution, the funds will be sent to the scammer's address. These attacks are especially effective because crypto addresses are long, and most people only check the first and last few characters.
Don't copy addresses from your transaction history and always verify the recipient's full address. For frequently used transfers, it's best to save verified addresses in your wallet's address book or use QR codes and official sources.
Cryptocurrency stolen: possible actions
Once funds have been withdrawn from a wallet, it's impossible to reverse a transaction on the blockchain. However, this doesn't mean no action is required. In some cases, some assets can be blocked or their subsequent movements can be tracked. A quick response and proper recording of the incident are key.
"These attacks don't happen out of the blue—they're planned. The attackers know what to do next even before the first breach. That's why delaying a response isn't just a waste of time, but a ceding of initiative to someone who already has it." — Ais Dorzhinov, co-founder of Match Systems.
The first step is to record all details of the theft. This information will be needed to analyze the movement of funds, contact the service's support team, and initiate a possible investigation. If there's a possibility that the stolen funds will be withdrawn through centralized exchanges, it's a good idea to contact their support services. Some platforms may temporarily freeze funds if they were received at known addresses belonging to the attackers and if there is confirmation of the theft. You can also notify blockchain analytics services or project security teams that monitor suspicious transactions and interact with crypto platforms.
Since most blockchains are public, asset movements can be monitored in real time using blockchain explorers and analytical tools. Experts analyze the transaction chain, identify associated addresses, and attempt to pinpoint points where funds can be converted or withdrawn. In some cases, connections to specific services can be established, increasing the likelihood of funds being blocked.
Recovering stolen cryptocurrency isn't always possible. However, the likelihood is higher if:
- the funds were quickly discovered and recorded;
- assets entered a centralized exchange or regulated platform;
- the attackers did not have time to carry out a complex chain of transactions to cover their tracks.
Even if it's not possible to fully recover funds, it's sometimes possible to freeze some assets or track their further movement. That's why it's important not to ignore the problem after an incident and to take action as quickly as possible.
Our experience: investigating thefts and recovering stolen funds
As the cryptocurrency industry evolves, not only financial instruments but also the schemes used by attackers are becoming more complex. With funds able to move across dozens of addresses on different blockchains and services in a matter of minutes, traditional monitoring tools are becoming insufficient. This is why companies specializing in blockchain analytics and incident investigations have become increasingly important in recent years.
One such solution is Match Systems. They are a team focused on tracking cryptocurrency transactions, analyzing complex fund chains, and identifying connections between addresses. Their work isn't limited to technical analytics. A significant portion of their processes involves practical support for investigations, interacting with exchanges, services, and other market participants to increase the likelihood of asset freezing.
FixedFloat has been collaborating with Match Systems for a long time, and over this period, the interaction has become regular and systematic. This collaboration involves a constant exchange of data on suspicious transactions, synchronization of case actions, and coordination in situations requiring rapid response. This format of collaboration allows us not only to record fund movements but also to build a comprehensive picture of the situation and act proactively.
During our collaboration, we have participated in the investigation of numerous crypto incidents, where, thanks to coordinated actions and blockchain analysis, we were able to track stolen assets, freeze the funds, and return them to the affected users. This is a comprehensive approach that combines analytics with effective communication with platforms and partners, ultimately enabling the process to achieve tangible results.
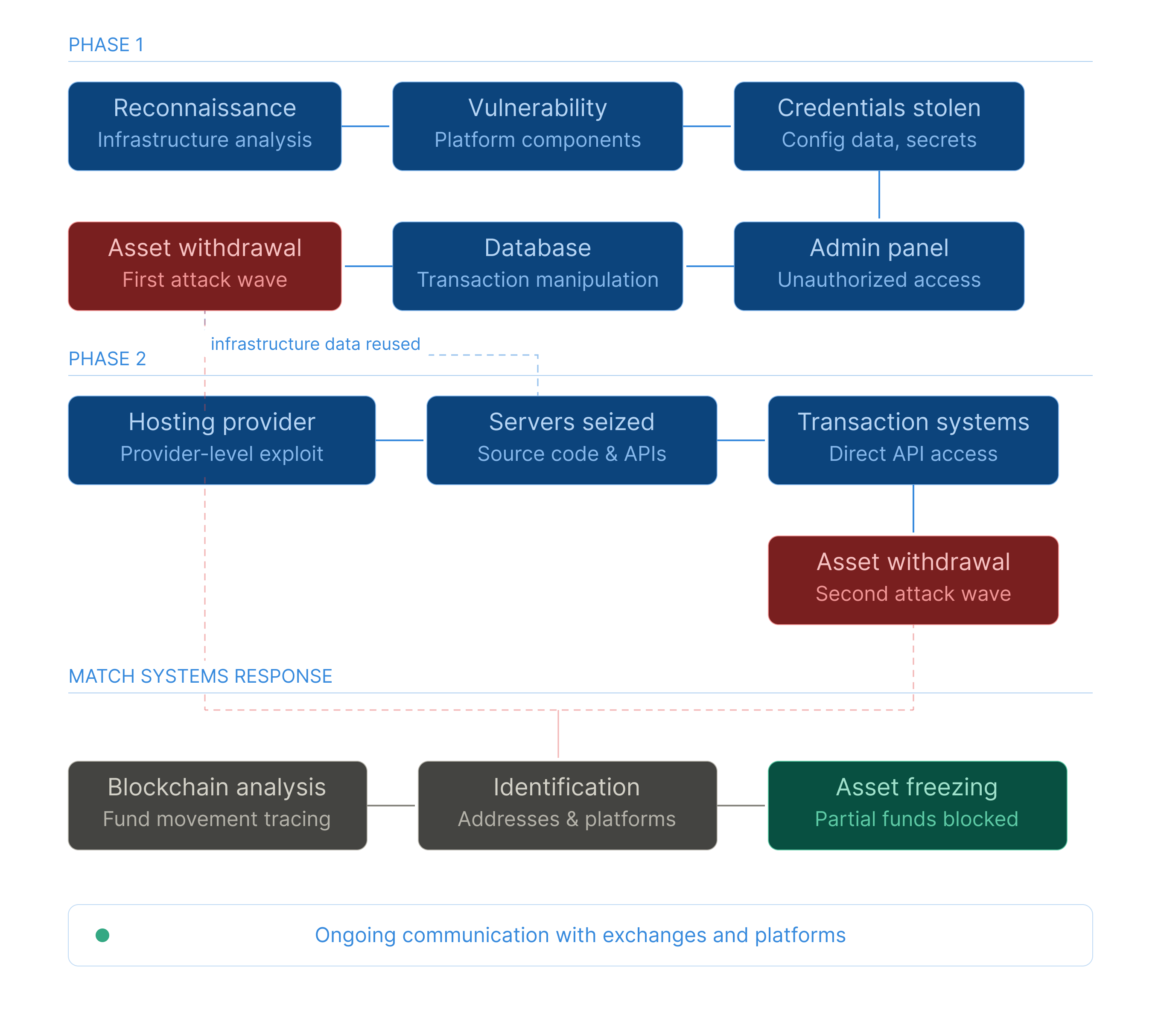
Between February and April 2024, our service was subjected to a series of targeted cyberattacks resulting in financial losses. Their multi-stage nature indicates a high level of sophistication on the part of the attackers, who conducted advance reconnaissance of the platform's infrastructure.
In the first stage, the attackers exploited vulnerabilities in infrastructure components, gaining unauthorized access to configuration data and administrative systems. The obtained credentials were used to penetrate the platform's administrative panel. Despite the protection of critical functions, access to the database allowed the attackers to manipulate transaction data and carry out unauthorized withdrawals of cryptocurrency assets.
In the second stage, the attackers, already armed with information about the platform's infrastructure obtained during the initial attack, compromised the server environment hosting auxiliary services. Exploiting vulnerabilities at the hosting provider level, they gained complete control over the servers containing the source code and internal APIs. This allowed them to directly interact with the platform's transaction systems and carry out additional thefts.
As part of the incident response, a comprehensive technical investigation was conducted, with the direct involvement of the Match Systems team. Specialists reconstructed the full attack chronology, established the compromise vectors, and identified the servers from which the malicious activity was carried out. At the same time, a detailed chain of movement of the stolen assets was constructed and subsequently tagged. A blockchain analysis allowed us to identify the withdrawal addresses and establish their links to specific services and platforms.
These measures allowed us to block some of the stolen coins on the platforms where they were received. We are currently continuing to work with the relevant services as part of our ongoing investigation into the incident. This case confirmed what we observe in most complex investigations: it's not the scale of the attack that determines the outcome, but the speed with which the analysis begins. Every hour after an incident is a narrowing window of opportunity. The attacker moves according to a predetermined plan. Countermeasures only work if they anticipate their next move.










